If your business sends promotional messages or commercial calls in Türkiye, IYS is part of the job. It sits at the intersection of consent management, campaign execution, customer trust, and audit readiness.
In practice, that means the issue is not only whether you collected an opt-in once. The real question is whether your records remain accurate and your opt-out process works on time. You also need to know whether every sending tool reflects the same permission status.
For SMEs, e-commerce companies, enterprise brands, and agencies, that difference matters. A weak IYS workflow can create legal exposure, damage campaign performance, overload operations, and weaken the customer experience. A disciplined workflow does the opposite: it protects revenue, improves list quality, and supports a more reliable communication strategy.
What IYS Compliance Actually Covers
IYS is Türkiye’s centralized permission platform for commercial electronic messages. It helps businesses manage SMS, email, and call permissions in a standardized way.
This creates a clearer and more consistent process. It also makes these records easier to track and verify. For recipients, it also creates a transparent way to review or reject permissions.
That sounds simple on paper, but the real situation is broader. In practice, there is more to manage than it first appears. IYS compliance covers how you collect consent and how clearly you define the communication channel.
It also covers how you keep proof, handle opt-out requests, and update the systems your team uses with that information. If your CRM says “opted in” but your campaign tool or call center database says something else, the problem is not theoretical. It is a workflow failure with compliance consequences.
This is why IYS is not something you handle once and forget. It is an ongoing operating model for permission-based communication. The moment your teams run campaigns from spreadsheets, reuse old lists, or leave opt-out updates trapped in one system, risk begins to build.
Legal Consequences of Ignoring IYS
Under Law No. 6563 and the related commercial electronic messaging framework, consent is the default rule. Businesses generally need prior approval before sending commercial electronic messages. Each message must also give the recipient an easy and free way to opt out of future communication. Once a recipient rejects communication, the sender must stop within the legally defined timeframe.
That alone is enough to make non-compliance expensive. The most obvious outcome is administrative fines. But the bigger issue is how quickly risk scales.
A single weak process can affect hundreds or thousands of records. That means one workflow mistake can become a costly compliance issue rather than a small isolated error.
Complaints also remain a live enforcement channel. Recipients can submit complaints through official channels, including e-Devlet-supported TİSS processes. These complaints may still trigger a review even after the original send date. This means a campaign that looked harmless when it launched can still generate legal exposure later.
A marketing list is not automatically a lawful list. If consent is missing, wrong, or not updated after an opt-out, the problem can grow fast. In that case, the communication may turn into a compliance problem.
There is also a data protection angle. Consent records involve personal data, so weak consent handling can create overlap with KVKK-related risk. If a company cannot show when and how it obtained consent, the issue becomes serious.
The problem can become more serious if the company keeps using personal data for marketing. This is especially true after the person has already withdrawn permission.
Commercial Risks You Feel Before the Fine Arrives
Many businesses focus on fines first because they are visible. In reality, the commercial damage often starts earlier. The source article itself correctly frames the issue as both a legal and a business risk, not just a penalty issue.
The first loss is trust. Customers notice when a company keeps sending messages after an unsubscribe request or uses the wrong channel.
They also notice when a company presents promotional content as a service update. That kind of framing can quickly damage trust. Even without regulatory action, that behavior can damage brand perception. It makes the company look careless, aggressive, or disorganized.
The second loss is campaign quality. Strong marketing depends on permission-based communication. When consent management is weak, list quality declines. That usually means lower open rates, weaker engagement, more spam complaints, and more wasted budget.
A list may look large on paper, but that does not always mean it is commercially strong. If a meaningful share of recipients never wanted the message, the list may have limited real value.
The third loss is message delivery performance. In other words, your messages may stop reaching people as expected. Spam complaints and unexpected messages can weaken email performance over time. Even legitimate communication may start landing in spam folders.
The damage can also continue beyond the campaign that caused the problem. In other words, poor IYS discipline can hurt both compliance and communication efficiency at the same time.
Technical Problems That Grow in the Background
Non-compliance is often a process problem before it becomes a legal problem. That is why technical risk and day-to-day process risk deserve separate attention. The source page points to the same pattern. Scattered data, delayed updates, and manual handling create the conditions for later violations.
A common failure point is fragmented data. Many teams collect permissions through checkout flows, pop-ups, call centers, store forms, or agency-managed campaign tools. Without one reliable permission model, differences appear quickly. Systems may start showing conflicting permission statuses.
A customer may have email permission but no SMS permission. Another may have opted out in one channel while still appearing active in another tool.
Manual handling makes that worse. When teams rely on spreadsheet uploads, one-off exports, or periodic list cleaning, the process becomes fragile.
Human error enters the workflow. Opt-out records may be missed. Channel labels may be wrong. Timestamps may be incomplete. Proof may be difficult to retrieve when needed.
Minimum IYS Control Loop
- Capture every opt-in and opt-out by channel.
- Store the timestamp, source, consent text, and an audit trail.
- Sync updates to IYS within the required window.
- Reconcile IYS status with your CRM, campaign tools, and call center data.
- Block sends immediately after an opt-out or mismatch.
- Review exception logs so failed updates do not sit unnoticed.
Another issue is audit readiness. If your team cannot easily show where consent came from or when it was recorded, that is already a risk.
The same is true if you cannot confirm that a rejection request was processed on time. The day-to-day workload also grows as scale increases. What works for a small list can break down fast at larger scale.
Common Mistakes That Turn Into Violations
Most IYS problems do not begin with intentional misconduct. They begin with habits that feel practical in the moment. The source article’s examples are useful precisely because they are everyday mistakes, not edge cases.
One common mistake is sending before registration or before the workflow is fully ready. Some companies assume a small campaign will go unnoticed. Others believe old customer relationships are enough. In practice, neither assumption creates a safe compliance basis.
Another frequent mistake is delayed updates. A team may collect consent through a form, a point-of-sale interaction, or a call center. It may then delay updating that information across systems.
That delay creates exposure because the internal record and the compliance record do not stay aligned. A similar issue appears when teams process opt-out requests too slowly.
A third mistake is treating unsubscribe mechanisms as optional details. Every commercial message needs a clear refusal path. A broken unsubscribe process turns poor user experience into direct compliance risk.
A fourth mistake is going beyond the given consent. Email permission does not automatically mean SMS permission. Consent for one campaign type does not automatically cover every later use case. When businesses stretch permission across channels or contexts, they create both legal and reputational problems.
A fifth mistake is assuming B2B means “no rules.” Some business recipients may be subject to different consent rules. However, that does not mean teams can ignore IYS governance or opt-out handling. Trusting a B2B exception too much is one of the easiest ways to create avoidable risk.
What Different Business Teams Should Do Next
If you are an SME
Keep the process simple and strict. Audit your current lists, remove records you cannot defend, and stop relying on memory or informal rules. Without in-house technical capacity, choose clarity and consistency over maximum flexibility.
If you run an e-commerce operation
Treat IYS as part of your revenue infrastructure, not just your legal stack. Checkout permissions, campaign tools, CRM records, and customer service actions must all reflect the same status. The more frequently you send, the more important automation becomes.
If you manage an enterprise brand
Focus on governance. Multi-brand structures, different teams, and multiple communication channels create more room for inconsistencies. Standardize the permission model, centralize the audit trail, and make sure every department works from the same rules.
If you are an agency
Do not assume the client’s data is usable just because it was handed over to you. Confirm channel scope, consent status, and opt-out handling before launch. Agencies often inherit risk from weak client-side processes, and that risk can surface during campaign execution.
How Makdos Helps You Manage IYS More Reliably
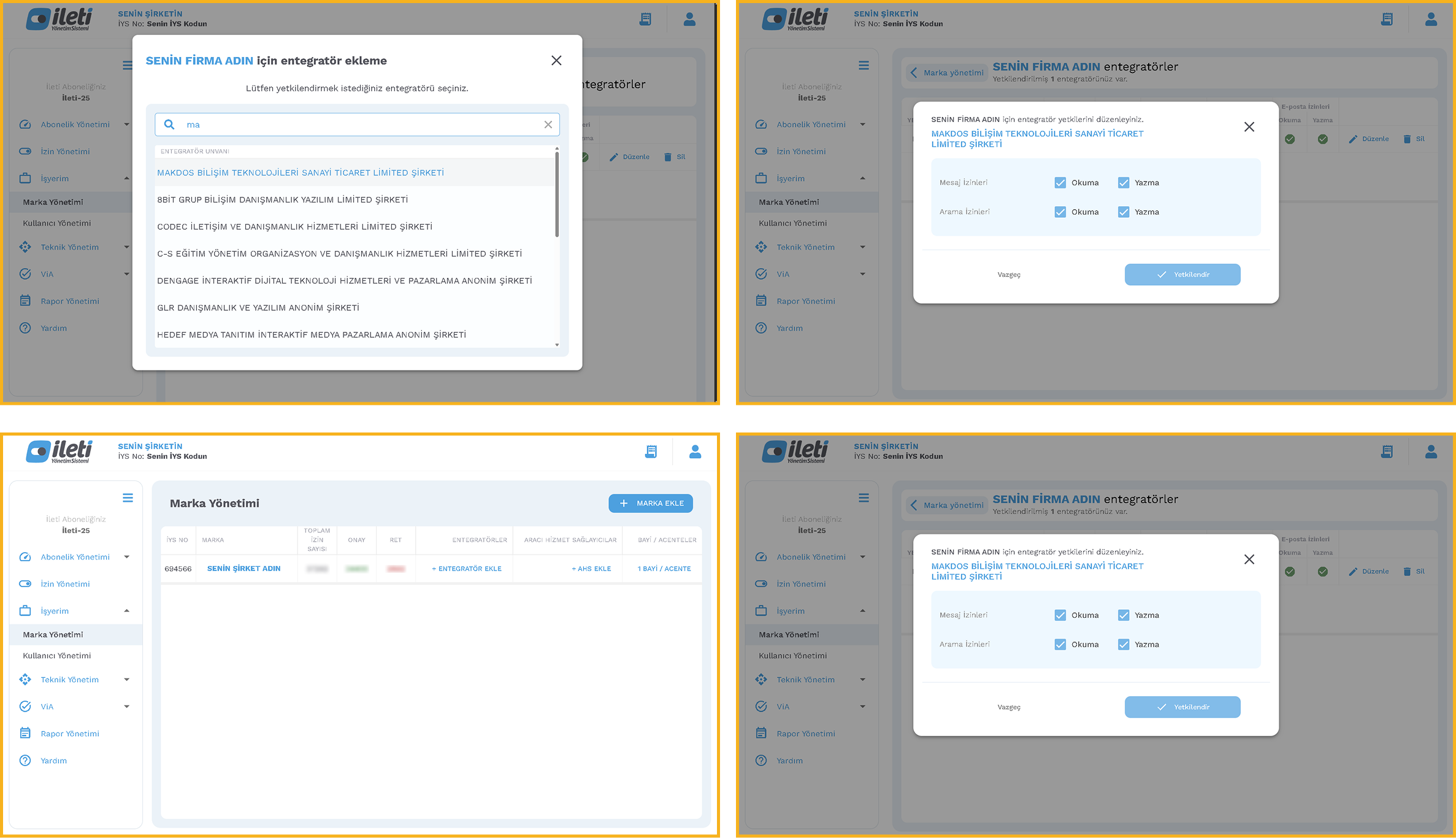
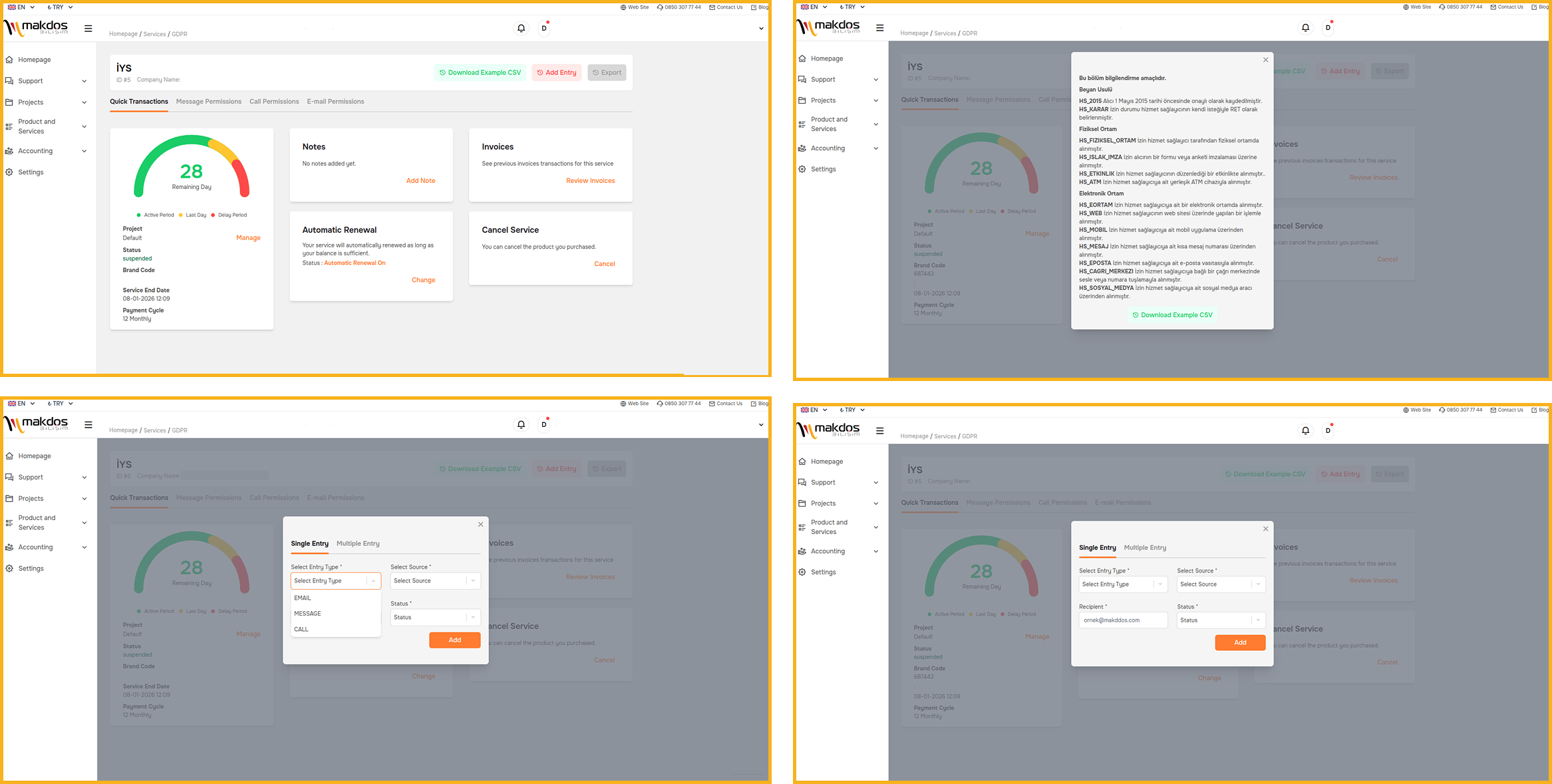
This is where the operational side becomes practical. Makdos offers IYS integration for businesses that want a more controlled way to manage consent and synchronization.
It also helps teams handle permission updates more clearly in daily use. Its English service and guide pages focus on two major needs. The first is reducing manual workload, and the second is keeping consent data aligned across systems.
For some teams, the right starting point is a panel-based workflow. That is useful when volumes are lower, updates are manageable, or the business wants a simpler onboarding model. For others, API integration is the better fit.
That approach is a better fit for businesses with frequent permission updates and multiple tools. It is also stronger for teams that need more automation and better data consistency.
Makdos also positions its IYS service around practical business use cases. The platform content highlights clear visibility into permissions by channel. It also focuses on synchronization between internal systems and IYS.
In addition, it supports workflows that connect CRM, e-commerce, and marketing tools. That matters because the core compliance problem is rarely “we did not know the rule.” It is usually “our systems did not stay aligned.”
If email is a major communication channel for your business, there is also a complementary infrastructure angle. A more disciplined permission workflow works better when it is supported by a structured mail environment. That environment should offer clearer administration, stronger access control, and better spam management. That is one reason Makdos Business E-Mail can complement an IYS-focused communication stack.
Conclusion
IYS non-compliance is rarely just a legal paperwork issue. It creates a chain reaction across fines, complaints, deliverability, customer trust, and operational workload. The longer a business depends on manual workarounds and inconsistent records, the more expensive the issue becomes.
The safer approach is straightforward. Collect clear consent, store proof, process opt-out requests on time, and keep every system synchronized. For SMEs, e-commerce brands, enterprise teams, and agencies, that difference matters. It determines whether IYS works as a background control layer or only becomes a concern after a problem appears.
If your workflow still depends on manual steps and scattered tools, now is the time to tighten the process. Makdos’s IYS service gives businesses a more structured way to manage permission data. It also helps reduce day-to-day friction and keep communication workflows more reliable as the business grows.

